Trade 24/7 Stocks, Crypto, and Forex*
Take on Wall Street with short-selling, fractional shares, 10x leverage, and zero commissions.



Best Investment App for Active Traders
Amazing features for pros and ease of use for everyone. Experience trading with zero fees and infinite liquidity.²

Buy Stocks on Weekends
Trade beyond pre-market and intraday. Act on breaking news over the weekend. Sell to save your gains, or buy a breakout stock before markets open.
Short Any Market
Profit in falling markets with short selling. Protect your portfolio the same way hedge funds do. With Morpher you pay zero interest fees on your shorts.


Invest with $1
Stop worrying about the price of Amazon stock or one ounce of gold. Invest the exact amount you want with fractional shares.³
Unlike Any Trading Brokerage
We rebuilt financial markets from the ground up on the Ethereum Blockchain. All in the pursuit of the perfect trading experience.
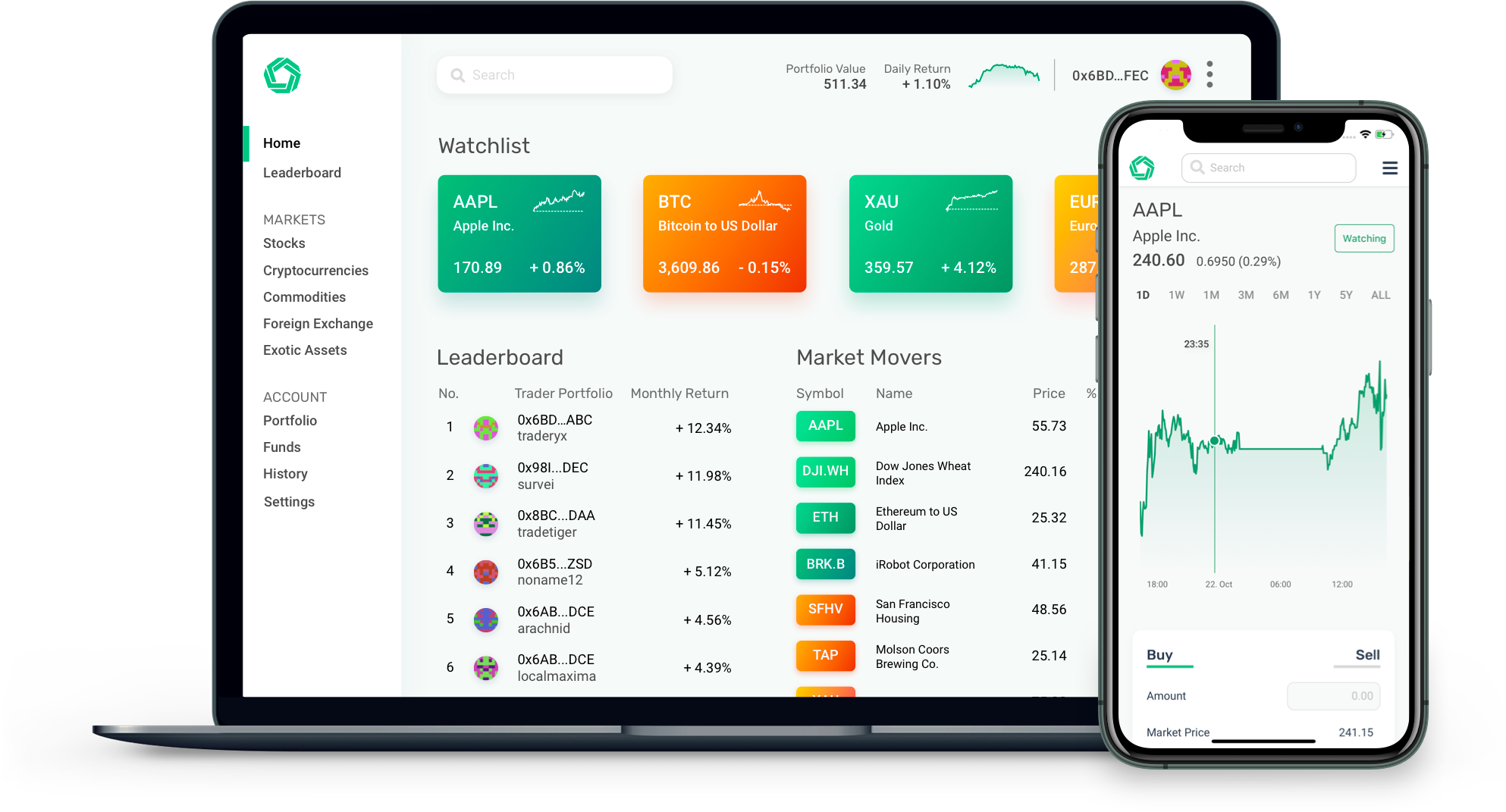
Zero Fees
Perfectly Liquid Markets
No Counterparties
Verifiable & Transparent Execution
Secured with Blockchain Technology
